Establishing Fairplay in Red Team engagements
Intro
During Red Team engagements, one of the most important tasks is to protect the crown jewels of the operation. As soon as the payloads prepared by the Red Team are delivered to the targets, security analysts of the Blue Teams submit potential malware samples to multiple online sources for further analysis. This is also common practice in multiple automated security solutions, such as email gateways, Antiviruses, sandbox frameworks and EDR products.
Many of these online sources can be queried using a file hash to identify whether a sample was previously analysed, as well as retrieve the results of such analysis. Also, most of them offer web-based APIs, that allow for the automation of such tasks.
Github repository: https://github.com/Hackcraft-Labs/Fairplay
Fairplay is an extensible modular framework that was developed by the Hackcraft Red Team, which aims to alleviate part of the heavy lifting of monitoring file hashes across multiple online-based sources, as well as provide an extensible way to generate notifications across multiple platforms.
When provided a list of file hashes to monitor, Fairplay will silently query its list of online sources, and provide notifications for when a sample is encountered (thus submitted for analysis) the first time, as well as for any submissions that follow on new sources, letting the Red Team know when their payload is analysed.
Possessing this information allows the Red Team to modify their attack paths, TTPs and overall strategy on the fly, according to analysis actions made by engineers or automated solutions. Since it was developed with extensibility in mind, and has been of help to the Red Team on multiple occasions, we decided to release it as open-source software.
Information regarding installing and configuring the tool can be found in its repository, along with a template configuration file in which API keys and webhook URLs can be specified. Examples of monitored IOCs are also provided.
Integrations
Fairplay currently supports monitoring of submissions on the following platforms, utilizing their web API:
- VirusTotal
- HybridAnalysis
- Google Search
- MetaDefender
- MalwareBazaar
Moreover, it supports generating notifications on the following services, using their webhooks:
- Microsoft Teams
- Slack
It also supports notifying directly to the console window.
Extensibility
Fairplay and its modules are developed in Python3. Instructions regarding the creation of new collectors (modules that query info in online sources) and notifiers (modules that generate notifications) can be found in Fairplay's repository and there is also support for retrieving "extra" information that are potentially provided by online sources, such as the detection type of the sample, how many engines detected is as malicious or clean, etc. "Hot" reloading of plugins and monitored IOCs is also supported, from its command-line interface.
Reported Information
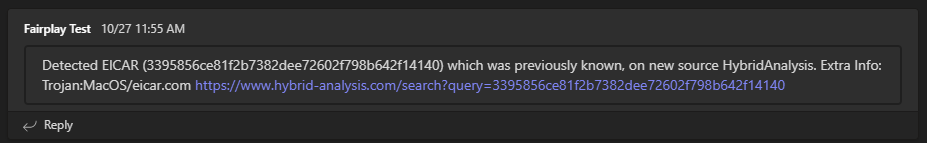
The following image is an example of a Microsoft Teams notification generated by Fairplay. In this example, the file hash of the popular antivirus test file 'EICAR' was identified for the first time on HybridAnalysis, for which Fairplay reports the detection type and provides a link to the submitted file for further observation.
Contributions
Contributions to the code base of Fairplay are very much welcome through Pull Requests submitted on its repository, both for the framework as well as for new modules that either collect information from a new online source or generate notifications on a new channel.